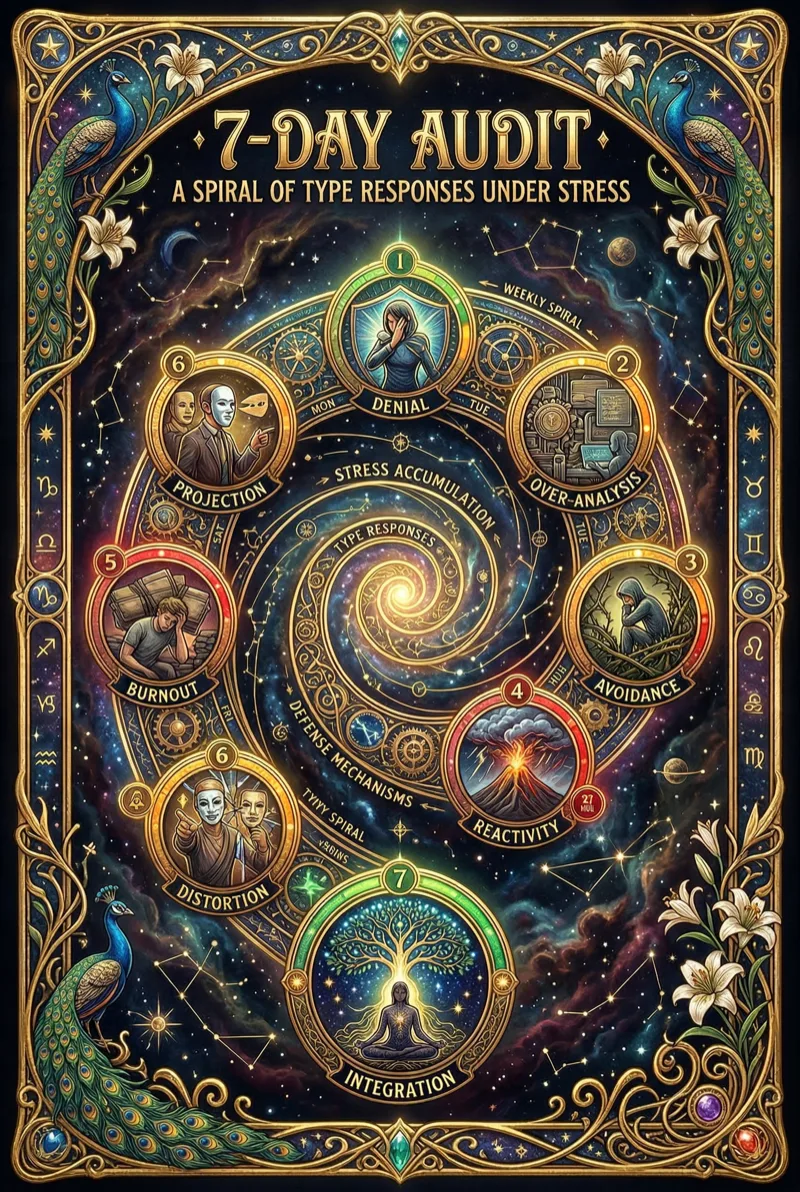
The Seven-Day Type Pressure Audit
Reading your type description is intake. Observing your type under pressure is diagnostics.
A personality quiz asks what you identify with. Pressure reveals what you do — the behavioral sequence that fires before identification begins. The sequence runs at approximately three hundred milliseconds. State speed, not story speed. By the time you narrate what happened, you have already executed the defense, already paid the cost, already moved on to the next stimulus without examining the transaction.
This protocol makes the transaction visible.
The Setup
You need three things:
- Your suspected Enneagram type.
- A logging system — a notes app, a physical notebook, a voice recorder. Anything that captures data with minimal friction.
- Seven days of paying attention to pressure moments. Not crises. Not breakdowns. Friction. The small activations that fire so quickly you normally miss them.
Every time something activates you — irritation, anxiety, the urge to withdraw, the impulse to perform, the compulsion to correct — log four fields:
Trigger | Signal | Defense | Cost
This is the same diagnostic structure used in pattern recognition work. Applied here specifically to type architecture.
Days 1-2: Mapping Triggers
Focus exclusively on the trigger column. Ignore the other three fields for the first two days.
The critical discipline is this: do not log the event. Log the class. Not “my coworker interrupted me during my presentation.” Instead: “someone questioned my competence” (Type 1). Not “my partner asked me to cancel my evening plans.” Instead: “someone needed more than I had budgeted for” (Type 5). Not “the team chose someone else’s proposal.” Instead: “someone ignored my contribution” (Type 3).
The event is noise. The class is signal.
By the end of Day 2, you should have six to ten entries. Review them. Look for the category that fires most frequently. Not the category that bothers you the most. The one that fires the most often. Frequency, not intensity, reveals the type’s surveillance system — the class of threat it was built to detect.
The surveillance system scans continuously, below conscious awareness, and activates when its specific threshold is crossed. You did not choose this threshold. Your nervous system installed it before your prefrontal cortex was fully myelinated. The trigger log makes the surveillance system’s specification visible.
Days 3-4: Tracing the Defense
Now add the defense column. After logging the trigger class, observe what happens next. The behavioral output — not the emotion, not the narrative, the behavior.
Type 5’s defense: retreat to analysis, reduce availability, hoard information. The system pulls inward, closes access ports, and begins processing the threat internally without external engagement.
Type 7’s defense: reframe, redirect, generate alternatives. The system produces options to avoid sitting with the discomfort. Every painful input is immediately converted into a plan, a possibility, a “what if.”
Type 1’s defense: correct, improve, internally narrate what should have happened. The system produces a revised version of reality in which the moral violation did not occur — not as fantasy, but as instructional material for next time.
The diagnostic key is speed. Watch for how fast each defense fires.
The fastest defense is the deepest groove. It is the one the nervous system installed first, refined through thousands of repetitions, and optimized until it runs below the threshold of conscious detection. Newer defenses are slow and deliberate — you can feel yourself choosing them. Original defenses are instantaneous — you discover them after the fact, through their consequences.
Days 5-6: Costing
Review the log. For each defense entry, add the cost column. Two questions:
What did the defense prevent? Connection. Risk. Expression. Vulnerability. Intimacy. Growth. The defense exists because it blocks something that the nervous system classified as dangerous. Name what it blocks.
What did the defense produce? Isolation. Rigidity. Exhaustion. Resentment. Missed opportunity. Relational damage. The defense does not operate for free. It has output — not just the blockage it creates, but the secondary effects that cascade through the system downstream.
Be specific. Not “I felt disconnected.” Instead: “I withdrew from the conversation and my partner went quiet for the rest of the evening. We did not speak again until morning. The silence produced a low-grade tension that affected the next two days.”
That is a cost. Not a feeling about a cost. The accounting is somatic and relational. The invoice is always specific.
Do not editorialize. Do not judge the defense as good or bad. Document it. The defense kept you alive — literally or psychologically — at some point in your developmental history. It is not malfunctioning. It is running a program that was appropriate for a context that no longer exists. The audit does not condemn the program. It reveals its current cost.
Day 7: The Map
Day 7 is reading day. No logging. No new data. Just review.
Lay out the week’s entries and look for three things:
The trigger category with the highest frequency. This is your type’s primary surveillance parameter — the class of input that your nervous system monitors most vigilantly. Not the thing that upsets you most. The thing your system scans for most persistently.
The defense with the fastest activation. This is your type’s core behavioral program — the response that has been refined through so many iterations that it executes before conscious awareness can intervene. This defense is not your personality. It is older than your personality. It is the behavioral substrate upon which your personality was constructed.
The cost with the widest downstream impact. This is your type’s structural liability — the chronic consequence that the defense produces, the bill that accumulates in domains you did not connect to the original activation. The cost is never local. It propagates through relationships, through energy levels, through the capacity for presence.
These three — most frequent trigger, fastest defense, widest cost — form a triangle. That triangle is the core of your type architecture. Not a label. Not an identity. A circuit diagram.
What the Audit Reveals
Seven days is not enough to fully map a type’s architecture. It is enough to make the architecture visible. The difference matters.
Visibility is not change. Seeing the defense does not stop the defense. It creates the precondition for eventual disengagement — a gap between trigger and response that grows wider with sustained observation. The gap does not eliminate the defense. It gives you the fraction of a second in which a different response becomes possible.
The Enneagram does not tell you who you are. Your nervous system under pressure tells you what it was built to do. This audit gives it seven days of honest observation and lets the data speak.
The data is not theoretical. It is your actual behavior, under your actual pressure, producing your actual costs. No interpretation is required. No framework is required beyond the four fields. The pattern will emerge from the log the way a function’s behavior emerges from its call stack — not because you imposed it, but because it was there all along, executing at a speed your narrative mind could not track.
Track it now. Seven days. Four fields. One map.
The rest is attention.